9 Ways To Get Secure VPS
Web hosting security is not only crucial for big organizations or fortune 300. In fact, information security should be a major concern for anyone having an online presence. strong password Those who do not take cyber threats seriously, are bound to face terrible consequences of destroyed websites, stolen personal information, and customer data loss.
How To Secure VPS ?
So today, we are going to talk about one of the critical security issues. Let’s address the major security measures you can take to secure VPS.
- Pay Attention To Your Default SSH Login & Password
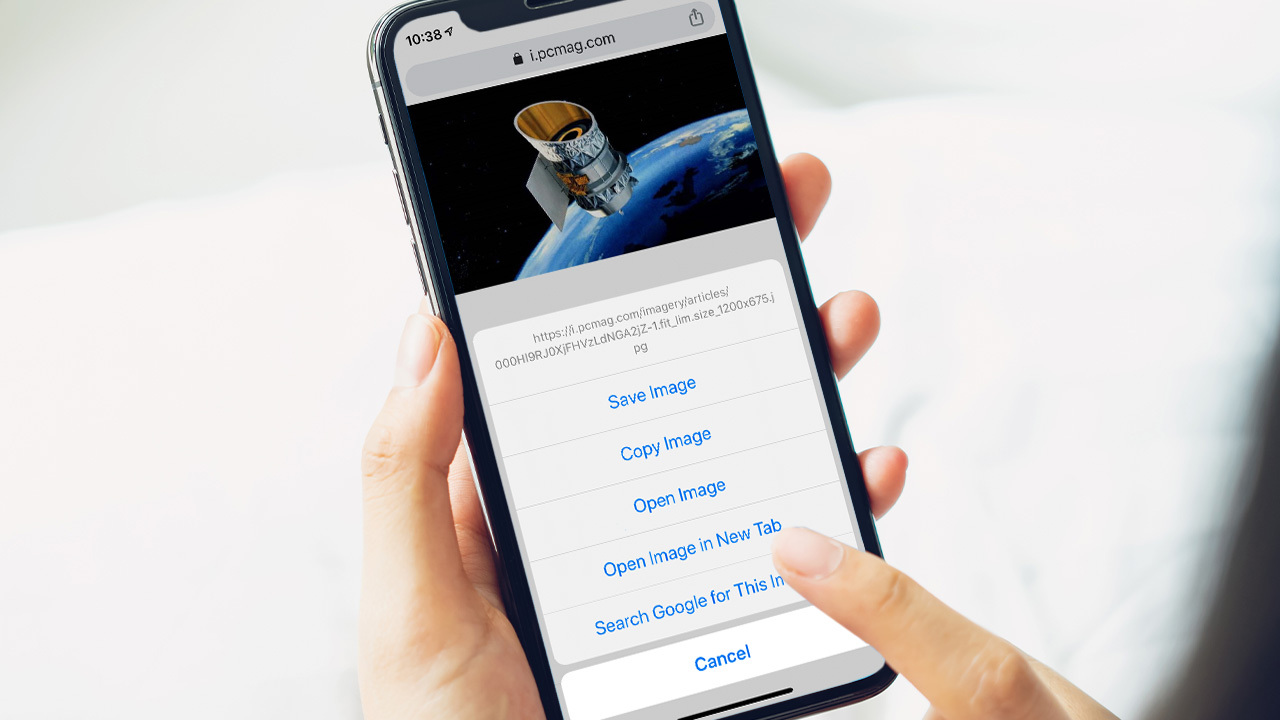
How do most VPS users log in to their servers? The answer of the majority will be via SSH, or Secure Shell, which is the right answer. It’s a method for connecting two computers remotely. But it may make you vulnerable to brute-force attack, a common type of attack, where hackers try a bunch of common passwords to get into your system.
Replacing the default SSH 22 port login password with a new and highly customized password is what security experts recommend. What makes a strong password is a combination of upper and lower-case letters, non-alphanumeric characters and numbers.
Here is the procedure to change it. Login to your VPS. Find the file /etc/ssh/sshd_config. Change the PermitRootLogin from the default YES to NO.
Those looking for more advanced security should consider SSH key authentication. It is also good at managing brute-force attacks. Or maybe, you can have just one dedicated IP that opens SSH. Also, you can use two-factor authentication.
- Zero Room for Outdated Software Versions
Old software versions bring nothing but vulnerability. Well, it does not take more than a few clicks to make necessary updates to your operating system and also, you may automate it.
- Monitor Your VPS Server Logs
You can have control over whatever happens with your VPS, if you manage your server logs properly. Tracking everything always helps you tackle the issues proactively, even before they surface.
So monitor traffic levels, user activity, software-generated errors, resource usage, and events as actively as you can. Setting up email notifications for warnings and errors is a good idea.
- Set Up Your Firewall
Firewall can help you block unwanted traffic. Luckily, majority linux-based operating systems come with preinstalled firewalls. Think about iptables, firewalld, ufw, DebianFirewall.
You can administer iptables and incorporate other control panels by installing the free ConfigServer Firewall, or CSF. There is an intuitive interface that helps you build up a secure VPS hosting UK. The interface even helps you manage the firewall settings.
- Secure VPS is Malware Protected
A firewall that keeps an eye on incoming traffic may also not be enough. Furthermore, you should think about motoring the files you upload to your VPS.
That makes the presence of any solid anti-virus software on your VPS mandatory. Also, you will be able to detect any suspicious activity.
- Brute-Force Protection
Yes, strong passwords give protection from brute-force attacks but they will not always be effective. In certain scenarios, hackers will still manage to get into your system.
You’ll need tools to identify brute-force assaults and prevent unauthorized logins. A feature integrated with cPanel. cPhulk is a good SEO example. BFA actually disables logins after a fixed number of failed attempts. The best thing is, it disables not only cPanel logins but also WHM, FTP logins. Email-based logins are also part of the list.
- Control User Access
Control distribution is also an important point in the journey of strengthening VPS. Control distribution means the areas where the users can operate.
Other than setting file permissions you should also consider tools like SELinux which is available with Red Hat Enterprise. They give you control over a lot of things. You have more than 100% control oncontrol process initializations and network interfaces. In addition you have control on files, and file systems along with user-management access.
Let’s consider the situation. You want to limit their access so they cannot affect the resource usage or change something in the sensitive data. The file systems CageFS (CloudLinux) or VirtFS can help you with this. They make sure that your users are isolated within a particular set of resources and files.
- Take Regular Backups
Backups are crucial irrespective of hosting type. Ideal way is to conduct them outside the server. Although some companies sell backup functionality as an add-on option.
- Block Countries Outside Your Market
If you are not operating in China, then any traffic coming from there could be a potential threat.
Also Read: bakugo