Electronic Document Signing and Cybersecurity
In today’s digital age, the use of electronic documents has become increasingly prevalent in both personal and professional settings. Electronic document signing has quickly become an indispensable component of daily operations for many organizations due to its convenience and efficiency; however, as we become more dependent on technology for daily business tasks, cyber threats and data breaches increase dramatically. Due to sensitive data being shared and stored electronically documents, it is vital that effective cybersecurity measures for electronic document signing be put in place. This is where electronic document signing comes in as it creates another opportunity to protect these valuable resources. Digital Signatures play a vital role in strengthening cybersecurity measures and guaranteeing the authenticity and integrity of documents being signed electronically. We will explore the world of electronic document signing and its related risks to cybersecurity. Additionally, we’ll cover ways organizations can secure their electronic documents against attacks from cyber criminals. By understanding all that goes into electronic document signing and cybersecurity is an invaluable way to stay ahead of competition while protecting valuable assets in digital space.
Importance of secure electronic document signing
Electronic document signing has become an indispensable tool in today’s globalized and interdependent society, used by businesses, government agencies and individuals alike. It enables efficient exchange of important information without needing physical paperwork. Yet with increasing cyber threats and data breaches it is imperative to implement secure document signing practices – this includes advanced encryption methods and authentication protocols. Taking this route protects organizations’ sensitive information from falling into inappropriate hands.
Secure electronic document signing not only protects confidential information, but it also helps preserve document integrity and validity. With electronic signatures it becomes nearly impossible to falsify documents, providing an efficient and trustworthy authentication method. This is particularly crucial when handling legal documents, contracts and other agreements that demand high levels of security and authentication. Secure electronic document signing reduces errors and ensures the accuracy of signed documents, saving organizations both time and resources. Furthermore, its efficient implementation enables faster turnaround times and increased productivity – two factors which cannot be overemphasized in today’s digital landscape. Organizations should prioritize implementing robust cybersecurity measures in order to safeguard their valuable information assets.
Protecting sensitive information from cyber threats
Due to cyber threats, protecting sensitive information has become a top priority for both individuals and organizations alike. With online transactions and document signing becoming more prevalent than ever, cybersecurity measures have never been more essential in protecting information from theft or loss. Hackers and cybercriminals are continually developing innovative methods for breaching confidential information, so both individuals and businesses need to remain vigilant when protecting their data. Prioritizing cybersecurity measures will allow individuals and organizations to mitigate cyber attacks while protecting sensitive data. By prioritizing cybersecurity measures, individuals and organizations can reduce the risks posed by cyber threats while maintaining confidentiality of sensitive data.
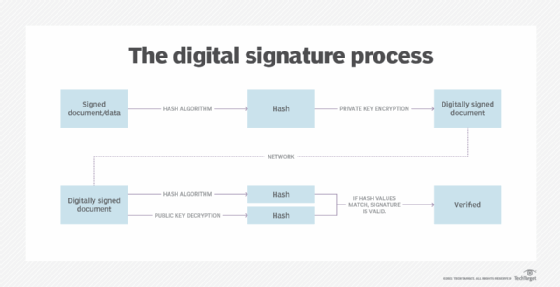
Ensuring authenticity and legal compliance
In order to enhance cybersecurity efforts, it is also crucial that efforts be directed toward verifying authenticity and legal compliance of electronic documents, verifying their originality and verifying they comply with relevant legal regulations and requirements. Organizations should implement electronic document signing processes which utilize digital signatures, encryption technology and other safeguards to verify the identity of signers and preserve document integrity. Additionally, it is crucial for organizations to remain up-to-date on the latest laws and regulations related to electronic documents, conducting regular audits to assess compliance with legal risks associated with them and ensure their security is optimal for meeting stakeholder expectations. By prioritizing both cybersecurity and legal compliance simultaneously, organizations can effectively secure sensitive data while upholding stakeholder trust.
Implementing robust encryption for secure transactions
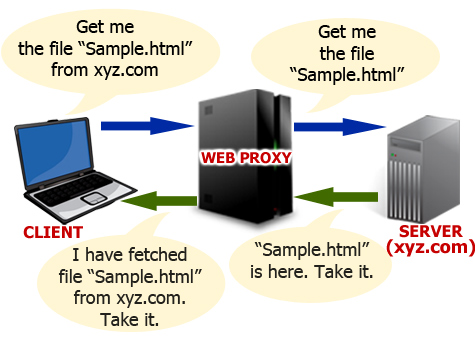
Organizations looking to strengthen cybersecurity and legal compliance should consider deploying robust encryption for transactions. Encryption is an integral element of data protection; it converts plain text into coded text which can only be decrypted with an authorized key, guaranteeing confidentiality, integrity, and authenticity for electronic documents and transactions. By employing advanced algorithms for encryption purposes, organizations can ensure secure transactions.
One of the key advantages of robust encryption is its ability to protect sensitive information from unauthorized access. Even in case of cyber attacks, an intruder won’t be able to untangle encrypted data; keeping sensitive files protected. Organizations handling sensitive or confidential information, such as personal data, financial records or trade secrets must take extreme precautions in protecting this data. Implementing robust encryption can also assist organizations with complying with data privacy laws and regulations, as it’s often required for protecting personal information. By prioritizing its implementation, organizations can significantly strengthen their cybersecurity efforts as well as ensure the secure transmission of electronic documents and transactions.
Safeguarding documents against unauthorized access
With so much sensitive data being stored and transmitted electronically, organizations must take proactive steps to safeguard documents against potential cyber threats – this may involve employing strong encryption methods so only authorized people have access to confidential data.
Encryption involves turning plain text into code that can only be deciphered using a specific key or password, making it near-impossible for unauthorised parties to gain access or manipulate documents containing confidential data. By employing encryption technology, organizations can reduce data breach risks and ensure legal regulations are followed – it should be prioritized as part of cybersecurity measures for any organization handling electronic documents.
Conclusion
Electronic document signing has quickly become an indispensable asset to businesses and organizations, offering greater efficiency and convenience for staff members. However, to protect sensitive information and avoid cyber attacks effectively, proper cybersecurity measures must be put into place and secure electronic signature platforms utilized. By adhering to best practices and using secure electronic signature platforms businesses can enjoy all the advantages associated with electronic document signing while staying aware of evolving threats against digital assets; using precautions when signing documents electronically could become invaluable in today’s fast-paced business world.